[ad_1]
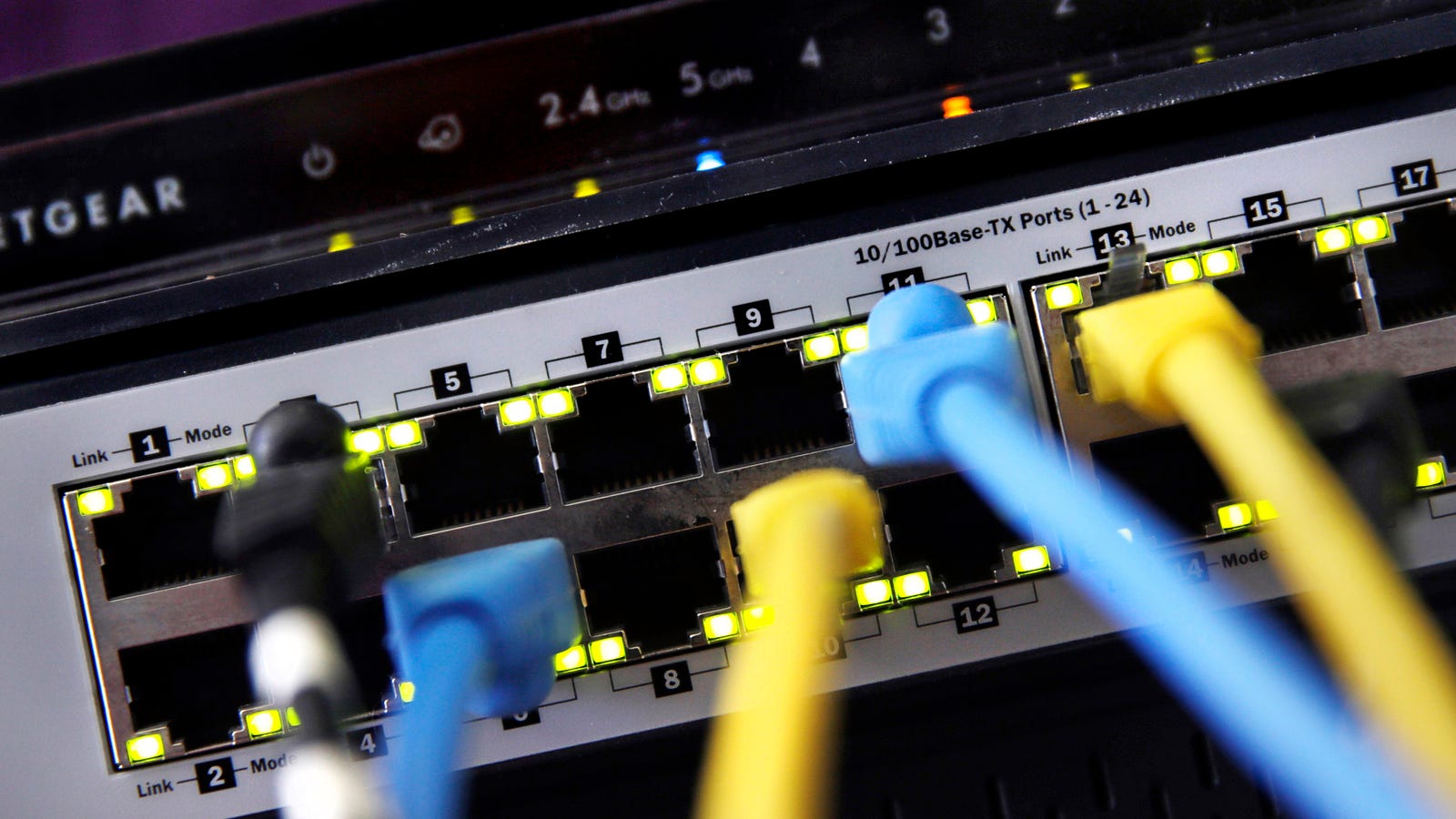
According to researchers, a hacker released a Microsoft exploit released last year after being removed from the National Security Agency to compromise more than 45,000 Internet routers.
Akamai, a cloud service provider and content delivery network, said in an article on Thursday that tens of thousands of routers had been compromised by attackers targeting vulnerable implementations of the Universal Plug and Play (UPnP) protocol. widely used allowing devices to recognize themselves automatically. through a local network.
Akamai said that on a reserve of 3.5 million devices, about 8% were using the vulnerable version of the UPnP.
"The victims of this attack will be at the mercy of the attackers because they will have machines on the Internet that were previously segmented and they have no idea what is going on," the company said. "In addition, network machines that had low patency priority will become easy choices."
UPnP has a long history of hackers, often exposing devices to the Internet that should only be visible locally. Akamai reported this summer that hackers were using the UPnP to conceal the traffic as part of an "organized and widespread abuse campaign".
The new attack – which exposes ports 139 and 445 – uses EternalBlue, a feat developed for the NSA, which was stolen and made public by the hacking group Shadow Brokers. This was later a component of the WannaCry ransomware attack and NotPetya wiper attack, which came under the name of ransomware (fakesomware?) But that came into reality of destroying shit.
Two weeks ago, Ars Technica, who for the first time reported on Akamai's research, explained how UPnP had been used to create a 100,000-router botnet. The mass infection was discovered by Netlab 360.
Unfortunately, researchers have been unable to say exactly what is happening with these 45,000 infected routers. But a successful attack, according to the researchers, "could generate a rich and targeted environment, paving the way for ransomware attacks or a persistent presence on the network."
Attackers can be discarded by keeping the firmware of the router properly updated and disabling UPnP. Akamai also recommends buying a new router after an infection. But if you're not expensive, simply disabling UPnP on an already infected router may not be enough; perform a factory reset for added security.
[Ars Technica]
[ad_2]
Source link