
[ad_1]
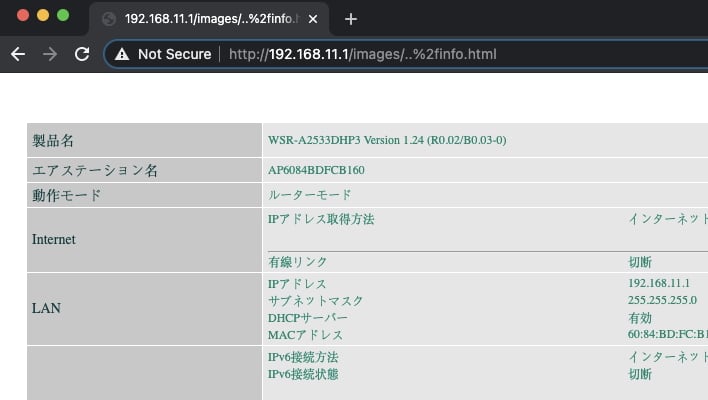
Tenable’s Evan Grant published research on August 3 that determined that anyone can bypass authentication on devices made by Arcadyan. In short, the problem stems from the router’s handling of URLs, in that it stops checking for bypass attempts as soon as it finds part of the URL in a bypass or whitelist.
Days later, Juniper Networks security researchers Mounir Hahad and Alex Burt “identified attack patterns that attempt to exploit this vulnerability in the wild from an IP address located in Wuhan, Saskatchewan. Hubei province, China ”. These active exploitation attempts appeared to be trying to deploy a Mirai botnet variant on the vulnerable routers we’ve listed below, courtesy of Tenable.
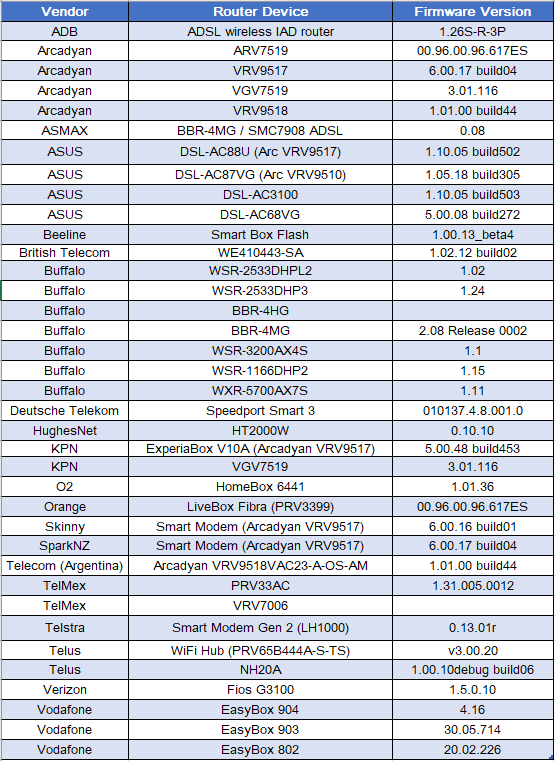
If your router is on the list above, you need to contact your router vendor, be it your ISP or the manufacturer itself, and find out how to fix the system. Having a whole new vulnerability exploited in the wild is incredibly concerning because people don’t have much time to react. Hopefully the router vendors act quickly and release an automatic update that fixes the issue, but in the meantime let us know if you’re affected in the comments below.
[ad_2]
Source link